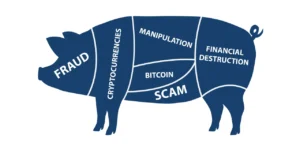
Unpacking the Complex Scheme: A Strategic Guide to Pig Butchering (‘Sha Zhu Pan’)
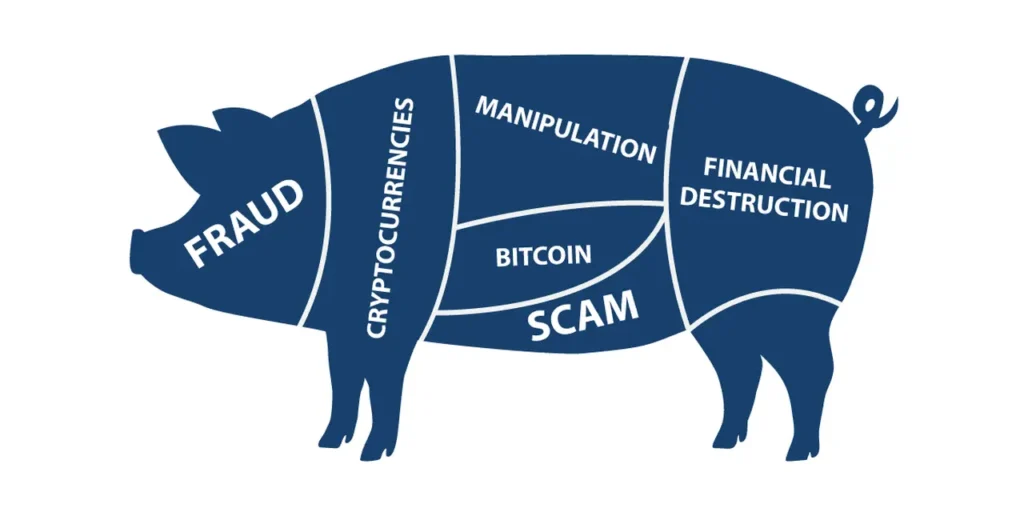
The Anatomy of a Digital Confidence Trap
In the landscape of modern financial crime, few operations are as psychologically devastating or structurally complex as the “Sha Zhu Pan”—literally translated as “Pig Butchering.” This moniker, derived from the criminal underworld, reflects the cynical methodology of the scammers: they fatten up the victim (the “pig”) with false promises and manufactured trust before the final slaughter. For cybersecurity professionals, financial investigators, and victims alike, understanding this scheme requires moving beyond simple definitions of fraud. It demands a recognition that this is a highly orchestrated, long-term socio-technical attack. Engaging in pig butchering scam recovery a is not merely a financial transaction; it is a forensic exercise in dismantling a sophisticated criminal enterprise disguised as a romantic or financial opportunity.
Beyond Romance: The Evolution of the Investment Scam
While early media coverage often categorized pig butchering solely as a “romance scam,” the modern iteration has evolved into something far more insidious. The contemporary “Sha Zhu Pan” operates less like a lonely-hearts con and more like a fully-fledged, dark-economy startup. Criminal networks, often concentrated in Southeast Asian Special Economic Zones (SEZs), operate with corporate efficiency. They utilize human trafficking to supply labor for “scam farms,” employ AI-driven language models to personalize outreach, and leverage legitimate-looking cryptocurrency exchanges to launder funds.
The process typically begins with a misdirected text message—a “wrong number” approach designed to initiate casual conversation. This initial contact is the most critical phase of the grooming process. The scammer does not mention money immediately. Instead, they invest weeks building rapport, sharing fabricated photos of luxurious lifestyles, and presenting themselves as a mentor figure who has mastered a “lucrative trading secret.”
The Technological Infrastructure of Deception
To understand how to dismantle these operations, one must first grasp the technological scaffolding that supports them. Scammers are no longer using clunky, unregulated websites. Instead, they deploy custom-coded applications that mirror legitimate trading platforms like Binance, Coinbase, or MetaTrader. These applications are often hosted on fast-changing domain names and utilize API integration to display real-time market data—except the data is a simulation controlled by the scammers.
When a victim makes an initial “investment” of a few hundred dollars, the platform usually allows a small withdrawal. This phase, known as “feeding the pig,” is designed to bypass the victim’s critical thinking. It creates a cognitive bias: the victim believes they have successfully withdrawn money, thus validating the legitimacy of the platform. However, the architecture is built to facilitate reverse engineering of the victim’s financial limits. Once the victim attempts to withdraw a substantial amount—or a principal sum in the six or seven figures—the liquidity dries up instantly.
Psychological Warfare and Cognitive Hijacking
The strategic guide to navigating this scheme must address the psychological grip it holds over victims. Unlike standard fraud where the victim realizes the deception quickly, pig butchering exploits the sunk cost fallacy to an extreme degree. Victims often remortgage homes, liquidate retirement funds, or borrow from family members because they are not merely investing; they are protecting the perceived relationship with their “mentor” or “partner.”
Furthermore, the criminals employ “exit scams” with brutal psychological precision. When the victim finally attempts to pull funds, the scammers often invent secondary fees—”taxes,” “security deposits,” or “liquidity fees”—to extract the last remaining assets from the victim. In many cases, even after the victim knows they have been defrauded, the scammer will continue communication, offering to “release” the funds for a final, smaller payment, thereby perpetuating the cycle of loss.
Read Also: Scam Awareness Tips: How to Recognize and Avoid Fraudulent Schemes
Strategic Countermeasures and Asset Tracing
For those affected, the path forward requires a shift from emotional reaction to strategic action. The immediate priority following the realization of fraud is the preservation of evidence. This includes:
- Complete Logs: Screenshots of conversations, including the scammer’s phone number, wallet addresses, and platform URLs.
- Blockchain Forensics: Because cryptocurrency is the primary vehicle for these scams, the transaction ledger is immutable. Forensic analysis can trace the flow of funds from the victim’s wallet through a series of “layering” wallets designed to obscure the final destination.
- Network Analysis: Identifying the points of ingress—whether it was a malicious ad, a social media DM, or a phone number—helps law enforcement connect the crime to larger syndicates.
It is critical to understand that recovery is not about “hacking” the scammers back. The decentralized and often jurisdictional no-man’s-land where these syndicates operate renders physical recovery attempts by amateurs dangerous. Instead, successful intervention relies on the speed of reporting to financial institutions and the utilization of certified blockchain investigators who can issue preservation orders or work with centralized exchanges to freeze funds that have not yet been fully laundered.
Regulatory Gaps and the Future of Cyber-Financial Crime
The prevalence of pig butchering schemes highlights a dangerous gap in global regulatory frameworks. While banks in Western nations have robust anti-money laundering (AML) protocols, the crypto sector—specifically decentralized finance (DeFi) and unregulated offshore exchanges—remains a weak link. Scammers exploit this regulatory arbitrage by moving funds through mixers, chain-hopping (converting Bitcoin to Monero to Tron), and utilizing “money mules” who are often victims of human trafficking themselves.
Looking forward, the strategy to combat “Sha Zhu Pan” must involve multi-lateral cooperation between telecom regulators to shut down SIM card farms, crypto exchanges to implement stricter Know Your Customer (KYC) protocols, and public awareness campaigns that focus on the pattern of the scam rather than just the topic of crypto.
Conclusion:
Navigating the aftermath of a pig butchering scheme is a journey that requires patience, technical expertise, and emotional fortitude. The architecture of the scam is designed to induce shame and isolation in the victim, which often leads to delayed reporting—the single biggest advantage for the criminal. However, the immutable nature of blockchain technology means that while the scammers may believe they are anonymous, they leave a permanent digital footprint.
To successfully reclaim agency after such an ordeal, victims must act swiftly to secure forensic evidence and engage with entities that understand the technical layers of these criminal enterprises. While the emotional and financial toll is immense, the window for asset recovery hinges on the speed and precision of the initial response. For those seeking to navigate this complex landscape, a structured approach to pig butchering scam recovery offers the only viable pathway to untangling the web of deception and moving toward financial resilience.